
“I want to be able to scan hashes of every file found by my EDR tool so I can quickly understand the threat they pose, and I don’t want to have to leave the EDR UI. Can you guys do that?”
This is a common question ReversingLabs gets from prospective customers. Those that are more security savvy add a further requirement, “Privacy matters to my company, so I do not want to rely on some crowd-sourced open site for file reputation.”
We all understand that security teams are dealing with both a critical lack of resources and an overload of potential cyberattack related events. In that light, these questions and requirements make a lot of sense — I do not want to be jumping from one pane of glass to the next because that is inefficient. I want as much context and intelligence around a security event as possible, available as quickly as possible so that I can make fast and accurate response decisions. I want to automate every detection and response process as I can, and I cannot sacrifice privacy or security.
This is where ReversingLabs technology shines. Our team's new EDR solution brief specifically talks to each of the requirements above in detail. More on that later. First, here's what security operations centers need to do to operate more effectively — and how ReversingLabs addresses those needs.
[ See solution brief: Enriching EDR Controls for Your SOC Analysts and Responders ]
Automation and efficiency
We understand that security teams run 10, 20, and even as many as 30 different security tools and that creates unwanted complexity. The ReversingLabs Spectra Platform is built with a broad set of APIs and has the ability to seamlessly integrate into your existing security tools. Because of the unique file and malware intelligence we provide, we enhance the performance and efficiency of almost all of your security tools. With EDR solutions, we can automatically display file intelligence results directly in the EDR UI. The Spectra Platform also has the ability to create and test YARA rules that define new malware (no AV signature). These rules can be exported to EDR solutions so that detection capabilities can be continually upgraded to find the latest threats.
Context and accuracy
ReversingLabs technology is powered by the industry’s most advanced automated static analysis engine which can reverse engineer almost any file or object to surface hidden malware. Over the years, ReversingLabs has amassed a sample set of over 8 billion goodware and malware files. The reputation and contextual data about each sample are not just AV engine results or dynamic analysis; although both are included, unlike any other solution, we have reverse engineered every file in the database, and it’s constantly curated. So not only do we offer the largest set of malware and goodware samples, we deliver the most in-depth intelligence about each file with the highest accuracy.
Static analysis produces some unique data about file structure and behavior – does this Word document make network connections? Does this harmless-looking PDF run shell scripts? Is this update properly signed by the vendor? – Results are obtained in milliseconds, without tying up expensive time and resources in sandboxing. Whether you send us a hash or sample, use our solution onsite and have your analysts reverse engineer files, or deliver our file intelligence service into your SOC products, the context and accuracy we provide will reduce the risk of advanced malware getting past your defenses.
Privacy
Between GDPR becoming the norm, and the recent privacy failures in the news from social media and cloud giants, privacy has become a board-level issue for all companies. ReversingLabs, a global company with offices and partners across Europe, North America, and Asia, shares these concerns. Privacy was built into the Spectra Platform from day one and includes the ability to deploy the complete solution onsite for our most private customers, but we also offer extensive privacy controls for customers of our cloud services including user-controlled privacy for hash or data uploads, and file sharing choice. Most importantly, our back-end research community is made up of a who’s who list of threat research teams at leading software vendors and research institutes. No hackers are testing their latest malware on our site or attempting to download sensitive data, our service is secure, private and GDPR compliant, and this includes our integrations with EDR solutions.
Put your focus back on EDR integration
For customers who are looking to enhance the capabilities of their EDR deployments, ReversingLabs fills the file/malware visibility gap offering the endpoint security analyst or SOC analyst detailed information on unknown risky files discovered on the endpoint. With immediate access to this file-level threat intelligence, analysts have the information they need to make quick decisions on containment and response actions. The screenshots below show the depth of information that can be displayed to the security analyst.
- Reputation: Is the file good, suspicious, malicious or unknown?
- Threat Name: Threat name of the queried sample.
- Threat level: How malicious a malware sample is; the higher the threat level, the greater the risk.
- Trust factor: Trustworthiness of a sample based on structural metadata and source of the file.
- Classification Type and Platform: Malware type and infection platform based on the latest analysis.
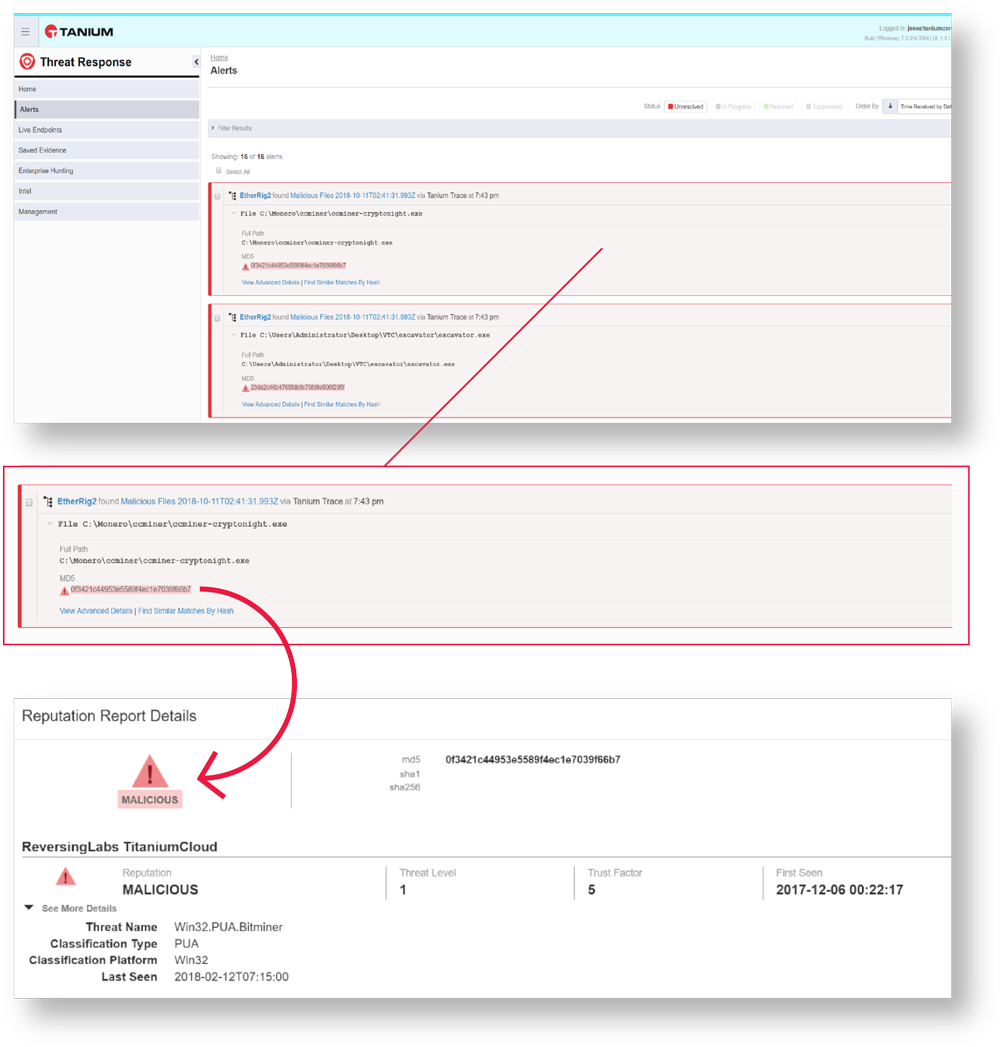
Views of ReversingLabs file context in EDR (Tanium) Interface
More indicators are available in the ReversingLabs Spectra Platform for more in-depth investigations and hunting activities. Analysts can easily pivot from the EDR UI into the ReversingLabs UI to find even more detailed information on the file to kickoff investigations. Deeper information includes:
- Malware type and family: Is the file related to any known malware types or family?
- Threat level: How malicious a malware sample is; the higher the threat level, the greater the risk.
- Classification source: Source of classification information.
- CVE: Common vulnerabilities and exposures related to this malware.
- Number and year: CVE number for vulnerability lookup.
- File identity hashes: How the file can be identified and searched on.
- AV Scanner match: The number of scanners that detected malware in the last scan.
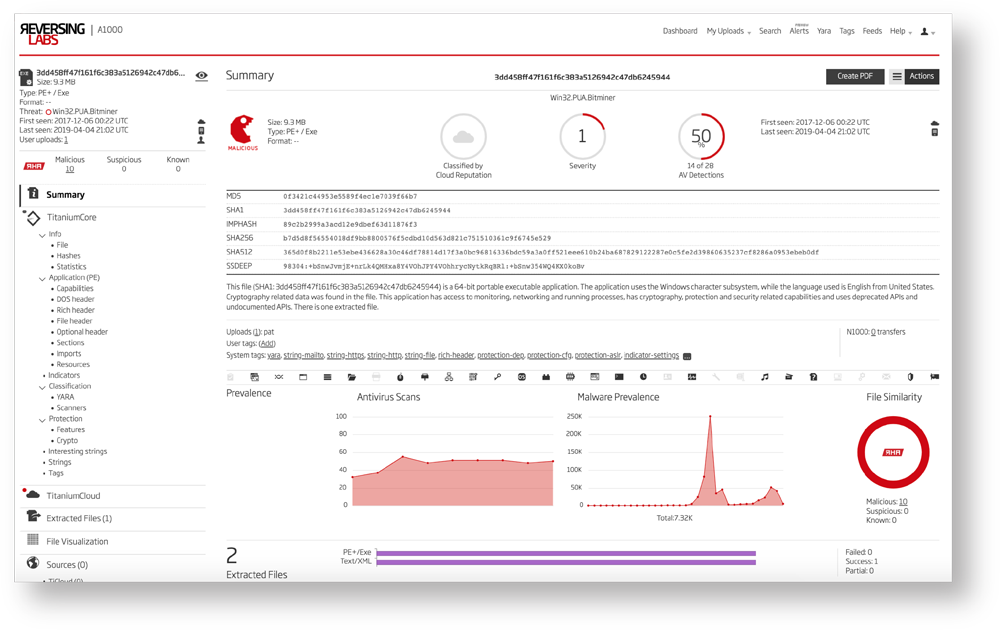 Spectra Analyze (formerly A1000): Detailed File Context View
Spectra Analyze (formerly A1000): Detailed File Context View
With malware context delivered into the EDR product, security analysts can quickly and accurately activate response playbooks. If the malware is found to be unknown, meaning new or polymorphic where no AV signature is available, the next step in the response process will likely be further investigation. Integration workflows allow an analyst to seamlessly move from the “file of interest” in the EDR UI to the same file within the ReversingLabs Spectra Platform. From there the file can be automatically decomposed and reverse engineered and a full static analysis performed.
Static analysis will surface all the malware related structures in the file, relationships to known malware functionality and family, and any evasion techniques that are discovered. The file can then be sent for further analysis in a sandbox, but with a much higher likelihood of successful execution since evasion techniques can be accounted for. In the end, even an unknown malware variant can be analyzed and the threat it poses understood. ReversingLabs takes you one step further. With a native YARA Rules Engine, a YARA rule can be built and tested in the ReversingLabs Spectra Platform. The YARA rule can then be imported into detection tools, including EDR products, so that the next time the unknown malware strikes, detection tools will immediately detect and identify it.
ReversingLabs integration with EDR products offers security teams a powerful solution to improve detection of advanced, even unknown malware on endpoints by automatically delivering file intelligence directly to the security analysts working in the EDR product. The accuracy and context of the file intelligence enable the security analyst to quickly and accurately identify and respond to the threat of increasing operational efficiency and reducing the risk of falling prey to a malware attack.
To learn more details about ReversingLabs EDR integration, including specific use cases covered and a customer case study, download our new EDR solution brief here. Plus, learn more about ReversingLabs' solution — and meet with us to learn how it supports the automation and optimization of your security operations center.







