Welcome to the latest edition of The Week in Cybersecurity, which brings you the latest headlines from both the world and our team about the most pressing topics in cybersecurity. This week: a new attack known as ‘Retbleed’ impacts microprocessors, journalists are becoming desirable targets for cybercriminals, and more.
This week’s top story
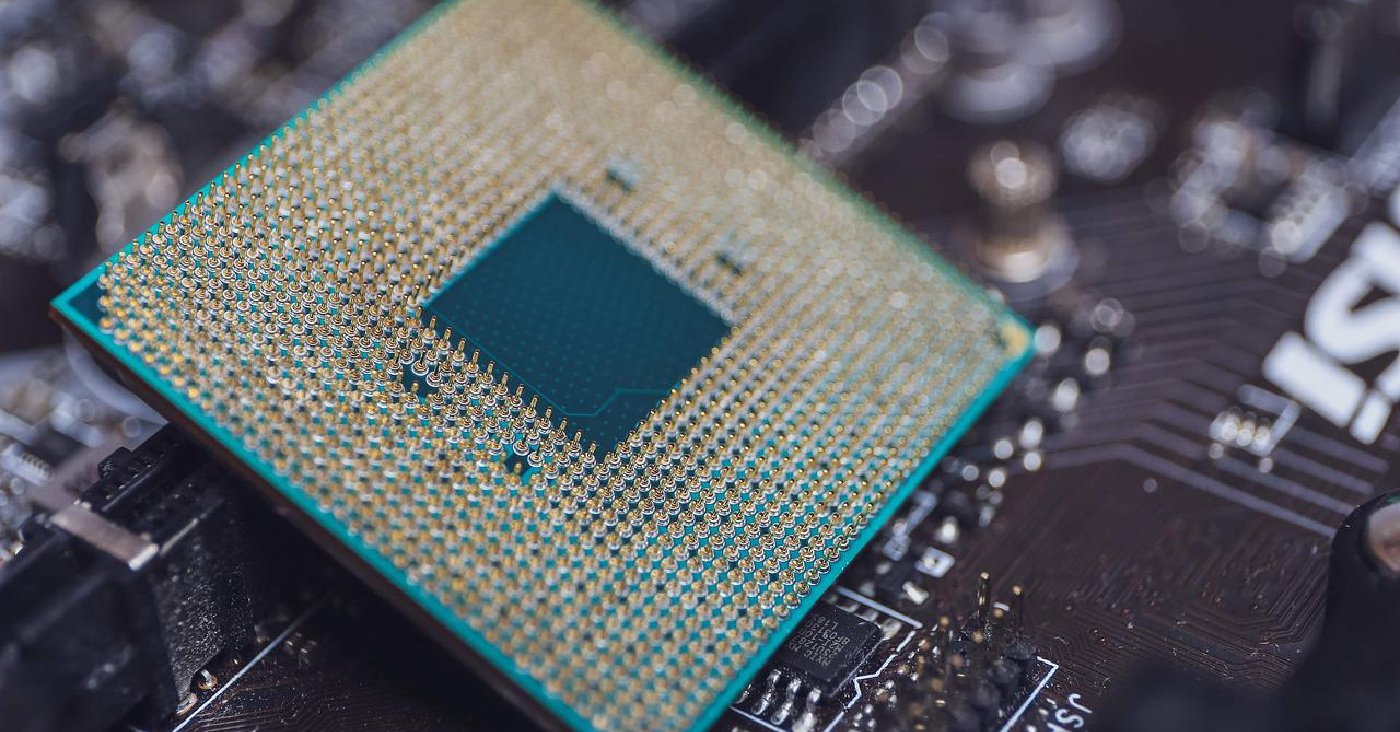
Microprocessors from Intel and AMD hit with data swiping ‘Retbleed’ attack
This week, researchers from the university ETH Zurich have discovered a speculative execution attack that can secretly leak password data and other sensitive materials from multiple kinds of Intel and AMD microprocessors. Researchers have named the attack “Retbleed,” because it specifically exploits Retpoline, a defensive software program created in 2018 that was meant to mitigate speculative execution attacks. Conclusive evidence now shows that the software was not fit to handle preventing these kinds of attacks.
This kind of attack takes advantage of a vulnerability in a CPU’s instruction process. In this process, CPUs encounter a direct or indirect instruction branch, which allows the CPU to predict the address for the next instruction they’ll receive, allowing the CPU to automatically execute it before the prediction is confirmed as correct. A speculative execution attack, also known as Spectre, will exploit this process by tricking the CPU into executing an instruction that accesses sensitive information, which normally would be off-limits. Once the operation is canceled by a threat actor, Retbleed extracts this sensitive data, successfully carrying out a Spectre-type attack.
There has been an on-going debate for years as to whether or not retpoline successfully mitigates speculative execution attacks. Some researchers came forward to share their hesitations about the software, while others, such as Linux creator Linus Torvals, rejected these hesitations. As a result of ETH Zurich’s research, it’s been proven that the retpoline software does not successfully mitigate Spectre attacks, as is the case with Retbleed.
Damage control has begun in the aftermath of this attack’s discovery. Both Intel and AMD have published advisories for Retbleed. It’s advised that any organization that relies on the affected CPUs should pay attention to the publications released by ETH Zurich on Retbleed, as well as see the mitigation guidance from both Intel and AMD.
News roundup
Here are the stories we’re paying attention to this week…
Journalists emerge as favored attack target for APTs (ThreatPost)
Targeted phishing attacks are traced to multiple threat actors who have each independently focused on stealing credentials and sensitive data and tracking the geolocation of journalists.
Cloud-based cryptocurrency mining attacks abuse GitHub actions and Azure VM (Security Affairs)
Threat actors are attempting to compromise a large number of cloud-based systems to mine cryptocurrency with a significant impact on target organizations in terms of resource consumption and cost.
European Central Bank head targeted in hacking attempt (Security Week)
The European Central Bank said Tuesday that its president, Christine Lagarde, was targeted in a hacking attempt but no information was compromised. The attempt took place “recently,” the Frankfurt-based central bank for the 19 countries that use the euro said.New UEFI firmware flaws impact over 70 Lenovo laptop models (BleepingComputer)
The UEFI firmware used in several laptops made by Lenovo is vulnerable to three buffer overflow vulnerabilities that could enable attackers to hijack the startup routine of Windows installations. Lenovo has issued a security advisory disclosing three medium severity vulnerabilities tracked as CVE-2022-1890, CVE-2022-1891, and CVE-2022-1892.
'Callback' phishing campaign impersonates security firms (ThreatPost)
A new callback phishing campaign is impersonating prominent security companies to try to trick potential victims into making a phone call that will instruct them to download malware.
Get up to speed on key trends and learn expert insights with The State of Software Supply Chain Security 2024. Plus: Explore RL Spectra Assure for software supply chain security.
Keep learning
- See Special Report: The State of Supply Chain Security 2024
- See Webinar: The new era of software supply chain security
- See Gartner's guidance on managing software supply chain risk
- Learn why/see buyer's guide: Upgrade your AppSec tools for the SSCS era
- See special and Webinar: CSF 2.0 and C-SCRM for Software Risk Management